Aws Firewall Vs Palo Alto

You know, I was chatting with a client the other day, a small startup, and they were telling me about their "firewall" setup. It was basically a glorified router with a few ports open to the internet, and their main concern was, "Will this stop the Nigerian prince emails?" Bless their hearts, they were trying their best, but the gap between their current reality and a truly secure environment was... well, it was a chasm. It got me thinking about the vast spectrum of what "firewall" means in today's world, from the DIY approach to the enterprise-grade beasts.
And that, my friends, is exactly why we're diving into the wild, wonderful world of AWS Firewalls versus Palo Alto Networks. It's not just about picking the "best" one; it's about understanding what each brings to the table and, more importantly, who they're actually for. Think of it like choosing a car. Are you a sensible sedan driver, or are you looking for a tricked-out sports car for a track day?
The Cloud Native Contender: AWS Firewalls
So, let's start with AWS. When you're already living and breathing in the Amazon Web Services cloud, their native firewall solutions are like the built-in GPS in your Tesla. They're integrated, they're designed to work seamlessly with the rest of the AWS ecosystem, and, let's be honest, they can be pretty darn appealing.
AWS offers a few flavors of firewall goodness. You've got your foundational AWS Network Firewall, which is your general-purpose network security service. It allows you to filter traffic at the network and application layers, kind of like a bouncer at a club, deciding who gets in and who stays out based on your rules. It’s stateful inspection, intrusion prevention, and web filtering – the whole nine yards, but served up in a way that’s meant to be managed within the AWS console.
Then there's AWS WAF (Web Application Firewall). This one’s a bit more specialized, focusing specifically on protecting your web applications from common web exploits. Think SQL injection, cross-site scripting, all those nasty things that can mess with your websites and APIs. It sits in front of your web servers, scrutinizing incoming requests like a hawk.
And let's not forget the trusty Security Groups and Network Access Control Lists (NACLs). These are more like the basic gatekeepers, operating at the instance and subnet level. They're fundamental, and honestly, you can’t really do much in AWS networking without them. They’re your first line of defense, and if you’ve ever spun up an EC2 instance, you’ve probably wrestled with them.
The big draw here for AWS Firewalls is, as I mentioned, the integration. If your entire infrastructure is built on AWS, managing your security within the same console, using the same IAM roles, and leveraging AWS's scalability is a massive advantage. You’re not dealing with separate vendors, separate licensing models (mostly!), or the headache of bridging on-premise and cloud security. It just… fits.
Plus, let's talk about scalability and cost-effectiveness. AWS is built for scale. If your traffic suddenly spikes, your AWS firewall can scale with it without you having to manually provision more hardware. And often, for cloud-native workloads, the pay-as-you-go model can be more economical than investing in hefty hardware upfront. This is where those startups I mentioned earlier might find their sweet spot, eventually.

However, it’s not all sunshine and rainbows. While AWS Firewalls are powerful, they can sometimes feel a bit… abstract. The configuration can get complex, especially for intricate security policies. And if you're coming from a traditional on-premise security background, the learning curve can be steep. It’s a different way of thinking about security, and sometimes, you just want that familiar physical box and its blinking lights, right?
The Enterprise Powerhouse: Palo Alto Networks
Now, let's switch gears and talk about the heavyweight champion, the seasoned veteran of network security: Palo Alto Networks. These guys have been in the game for a long time, building a reputation for their Next-Generation Firewalls (NGFWs) that are packed with features and a focus on application visibility and control.
Palo Alto’s philosophy is centered around knowing exactly what applications are running on your network, regardless of port or protocol. They don’t just see traffic; they see the application generating that traffic. This allows for much more granular control. You can allow "Facebook" but block "Facebook games," or permit "Salesforce" but restrict file uploads. It’s a level of insight that was once the stuff of IT fairy tales.
Their NGFWs come in hardware appliance form, virtual appliances, and also have cloud-delivered security services. So, whether you’re a massive data center with racks of servers or you're starting to dip your toes into the cloud, they have a solution. They’re known for their robust threat prevention capabilities, including intrusion prevention, advanced threat protection (ATP), and wild-fire analysis for zero-day threats.
One of the biggest selling points of Palo Alto is its unified platform. They aim to consolidate various security functions – firewalling, intrusion prevention, threat intelligence, URL filtering, application control – into a single, manageable device or service. This can simplify operations and reduce the number of disparate security tools you need to deploy and manage.
For organizations that have a complex, hybrid, or purely on-premise environment, Palo Alto often shines. They offer deep visibility into traffic that might otherwise be hidden. Their GlobalProtect solution, for instance, provides robust endpoint security and secure remote access, which is crucial for any organization with a mobile workforce.

But here’s the thing about enterprise-grade solutions: they often come with a hefty price tag. Palo Alto Networks hardware and licensing can be a significant investment. And while their platform is powerful, it can also be complex to set up and manage, often requiring specialized expertise. You’re not just plugging it in and hoping for the best; you’re likely going to need trained professionals to get the most out of it.
AWS Firewall vs. Palo Alto: The Showdown
So, when we put them head-to-head, what are the key differences and considerations?
Use Case and Environment
This is perhaps the most critical factor. If your entire world exists within AWS and you're looking for a tightly integrated, cloud-native security solution that scales with your cloud footprint, then AWS Firewalls are a very strong contender. They are designed to work with VPCs, subnets, and other AWS services natively.
If you have a hybrid environment, a significant on-premise presence, or you need extremely granular control over applications that might be harder to identify in a pure cloud context, Palo Alto Networks often makes more sense. Their strength lies in their ability to provide deep visibility and control across diverse network architectures.
Complexity and Management
AWS Firewalls, while powerful, can have a steeper learning curve for those unfamiliar with the AWS ecosystem. The management is done through the AWS console or APIs. It’s integrated, but it’s also abstract. You need to understand AWS networking concepts deeply.
/filters:no_upscale()/news/2022/04/aws-palo-alto-firewall/en/resources/1Cloud NGFW for AWS Architectural Block Diagram-1649308899566.png)
Palo Alto Networks, on the other hand, offers a more traditional management interface, often with a graphical user interface (GUI) that many network security professionals are accustomed to. However, the sheer depth of features means it still requires significant expertise to configure and manage effectively. It’s powerful, but not necessarily "simpler" in terms of overall operational overhead.
Features and Granularity
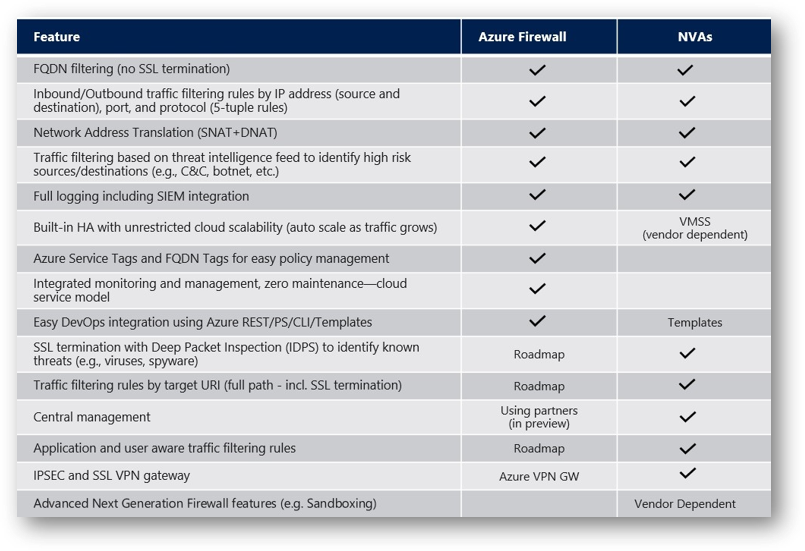
Palo Alto has historically been the king of granular application identification and control. Their ability to see and control applications regardless of port and protocol is a major differentiator. This is crucial for compliance, data loss prevention, and enforcing shadow IT policies.
AWS Network Firewall is catching up rapidly. It offers application-layer filtering and intrusion prevention. However, the depth of application identification might not always match Palo Alto's specialized engine. AWS WAF is excellent for web applications specifically, but it's a different beast than a full network firewall.
Cost
AWS Firewalls, especially for cloud-native workloads, can be very cost-effective. The pay-as-you-go model, combined with AWS's inherent scalability, can mean you only pay for what you use. This is a huge plus for startups and companies with fluctuating traffic.
Palo Alto Networks, especially their hardware appliances, represent a significant upfront investment. While they offer cloud-delivered options which can shift the cost model, it's generally considered a more premium solution with a higher total cost of ownership.
Integration and Ecosystem
This is where AWS Firewalls really shine for AWS users. Seamless integration with IAM, CloudWatch, other AWS services – it’s a dream for those deeply embedded in the AWS cloud. You can automate a lot of security tasks.
Palo Alto offers integration with various third-party security tools and platforms, and their own cloud services aim for comprehensive security. However, it’s less about native integration within a single cloud provider’s ecosystem and more about building a robust security fabric that can span multiple environments.
The Verdict? It Depends!
Honestly, there's no single "winner." The best firewall for you depends entirely on your specific needs, your existing infrastructure, your budget, and your team's expertise.
If you're all-in on AWS, a cloud-native company, and you value seamless integration and scalability, then AWS Firewalls are an excellent choice. They’re powerful, cost-effective in the cloud, and will integrate beautifully with your existing AWS services. You’ll need to embrace the AWS way of doing things, of course.
If you have a complex, hybrid environment, require deep application visibility and control across diverse networks, or are looking for a seasoned, feature-rich, enterprise-grade solution, then Palo Alto Networks is a very compelling option. They offer a robust, unified platform that’s been battle-tested.
And what about that startup with the Nigerian prince problem? Well, they'll probably start with the basics – good user education and maybe a cloud-based email security solution. But as they grow, and as their AWS footprint expands, they might find themselves looking at AWS Network Firewall. If they go the hybrid route, or have very specific application needs, then Palo Alto might enter the picture later down the line.
The most important takeaway? Understand your own requirements first. Don't just pick a vendor because they have a cool logo or a flashy marketing campaign. Dive deep into what you need to protect, how you need to protect it, and what resources you have available. Then, and only then, can you make an informed decision that will keep those Nigerian princes (and far more serious threats) firmly outside your digital gates.
