Can An Individual Be Held Responsible For A Data Breach
Imagine you've got your secret cookie recipe. It's the one that makes your grandma weep with joy and your friends beg for the secret ingredient (which, of course, is love... and maybe a pinch of extra butter). Now, what if your neighbor, who’s been admiring your baking from afar, accidentally bumps into your kitchen door, and your recipe card, scribbled on a napkin, flutters out and into the wind? Uh oh.
That’s kind of like a data breach, but instead of cookies, we’re talking about all sorts of personal information. Think of your online accounts like a digital pantry filled with your favorite things: your email address, your passwords, maybe even your credit card details (hopefully not!). When a data breach happens, it’s like that recipe card getting blown away, but on a much, much bigger scale. Sensitive stuff can fall into the wrong hands.
Now, the big question on everyone’s mind is: can you, a regular person just trying to live your life, get in trouble for a data breach? The answer is a surprising and sometimes downright funny, yes! But before you start panicking and hiding your computer under a pile of laundry, let’s break it down. We’re not talking about accidentally leaving your front door unlocked and a squirrel stealing your nuts. We’re talking about situations where your actions, or sometimes your inactions, can have consequences.
The Case of the Overly Enthusiastic Sharer
Meet Brenda. Brenda loves sharing. She shares her vacation photos, her lunch menu, her cat’s latest antics, and, unfortunately, sometimes a little too much personal information online. Imagine Brenda posting a picture of her new work ID badge on social media. It’s got her name, her job title, and yes, even her employee ID number. She thinks it’s cute! Her friends “like” it. But what Brenda doesn’t realize is that this little piece of information, combined with other easily accessible tidbits, could be a golden ticket for someone with less-than-honorable intentions. If a hacker uses Brenda’s employee ID to gain access to her company’s systems, Brenda, through her enthusiastic sharing, could find herself in a bit of a pickle. It’s not malicious, but it’s certainly not helpful!
The "Password is Password123" Party
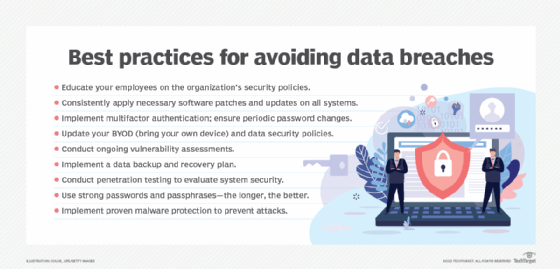
Then there’s Gary. Gary believes in simplicity. He’s got a password for everything, and it's always the same: Password123. He even uses it for his bank account. Gary figures, “Why make it complicated? I’ll never forget it!” Unfortunately, hackers love simplicity. If Gary’s email account gets compromised (because Password123 is the first thing anyone tries), and he uses that same email and password for his online shopping or even, heaven forbid, his doctor’s portal, then Gary has inadvertently opened the floodgates. This isn't about Gary being a bad guy; it's about Gary’s password choices being… well, let’s just say less than secure. If a breach occurs because a hacker brute-forced Gary’s extremely predictable password and then used that access to get to more sensitive data, Gary might be on the hook for not taking reasonable steps to protect his own information.
"It's not about being a criminal, it's about being a bit too 'neighborly' with your digital door."
The Accidental Architect of Chaos
Sometimes, it’s not even about passwords or oversharing. Think about Chloe. Chloe works from a coffee shop a lot. She’s a whiz with her laptop, but she’s also a bit of a multitasker. While she’s emailing sensitive client information, she’s also downloading a dodgy-looking free game and clicking on every pop-up ad that appears. Suddenly, her laptop is behaving strangely. It’s slow, it’s showing weird messages, and her antivirus software is screaming. Unbeknownst to Chloe, that free game or one of those ads had a sneaky little passenger – malware. This malware then quietly siphoned off all the sensitive client data Chloe was working with. Now, Chloe hasn’t intentionally given the data away, but her clicking habits have indirectly caused a massive breach. In this scenario, Chloe could be held responsible, especially if her employer has strict guidelines about downloading software or clicking on suspicious links. It’s like leaving your valuable recipe book on a park bench and a flock of pigeons decide to have a picnic on it.

The Heartwarming (and Slightly Embarrassing) Reminder
And then there are the truly heartwarming, yet ultimately cautionary tales. Imagine Uncle Bob. Uncle Bob, bless his heart, is not exactly a tech guru. He gets an email that looks exactly like it’s from his bank, asking him to click a link to “verify his account details.” He’s just trying to be helpful and make sure his account is up-to-date. He clicks. Turns out, it was a phishing scam. Uncle Bob, in his earnest desire to be a good customer, has just handed over his login credentials to a scammer. If this leads to a breach of his bank’s systems (or, more likely, his own personal account and then potentially others he’s linked to), Uncle Bob, through his well-intentioned but misdirected actions, could be facing some uncomfortable conversations.
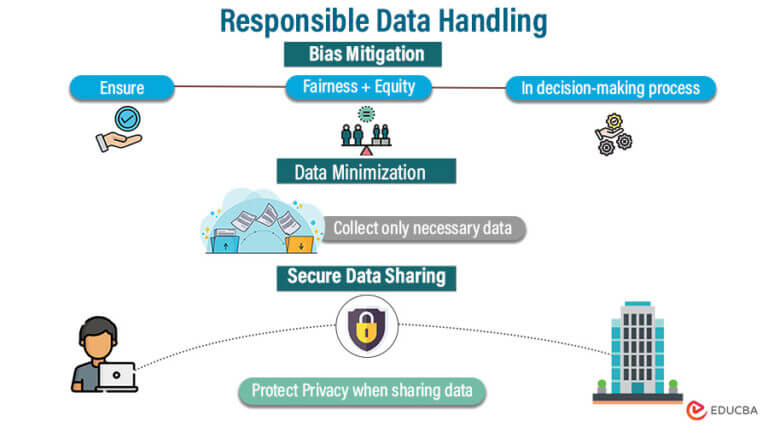
The takeaway here isn't to live in fear or to shun technology. It's to be mindful. Think of your online information like your prized possessions. You wouldn't leave your wallet on a bus seat, would you? Similarly, you need to take reasonable steps to protect your digital world. This means using strong, unique passwords (maybe a password manager can be your digital butler!), being wary of suspicious emails and links, and thinking twice before sharing sensitive information publicly. It’s about being a responsible digital citizen, making sure your online pantry is locked up tight, and that your secret cookie recipe stays safe and sound!
