Cisco Asa 9.6 Packet Flow
Okay, so we're going to talk about something that sounds about as exciting as watching paint dry. But stick with me, because even the driest of topics can have a little sparkle if you squint just right. We're diving headfirst, or maybe just dipping a toe, into the magical world of Cisco ASA 9.6 packet flow. Yes, you read that right. Packet flow. Try not to snooze just yet!
Imagine your network is a super-fancy, heavily guarded castle. And packets? Those are like tiny little messengers, carrying all sorts of important information. They’re zipping around, trying to get from Point A to Point B. But our castle, represented by the mighty Cisco ASA, has a very specific way of handling these messengers. It’s like a bouncer at a VIP club, but instead of checking IDs, it’s checking packets.
The Cisco ASA is basically the ultimate security guard for your network. It's seen it all. It's heard it all. And it's definitely inspected it all.
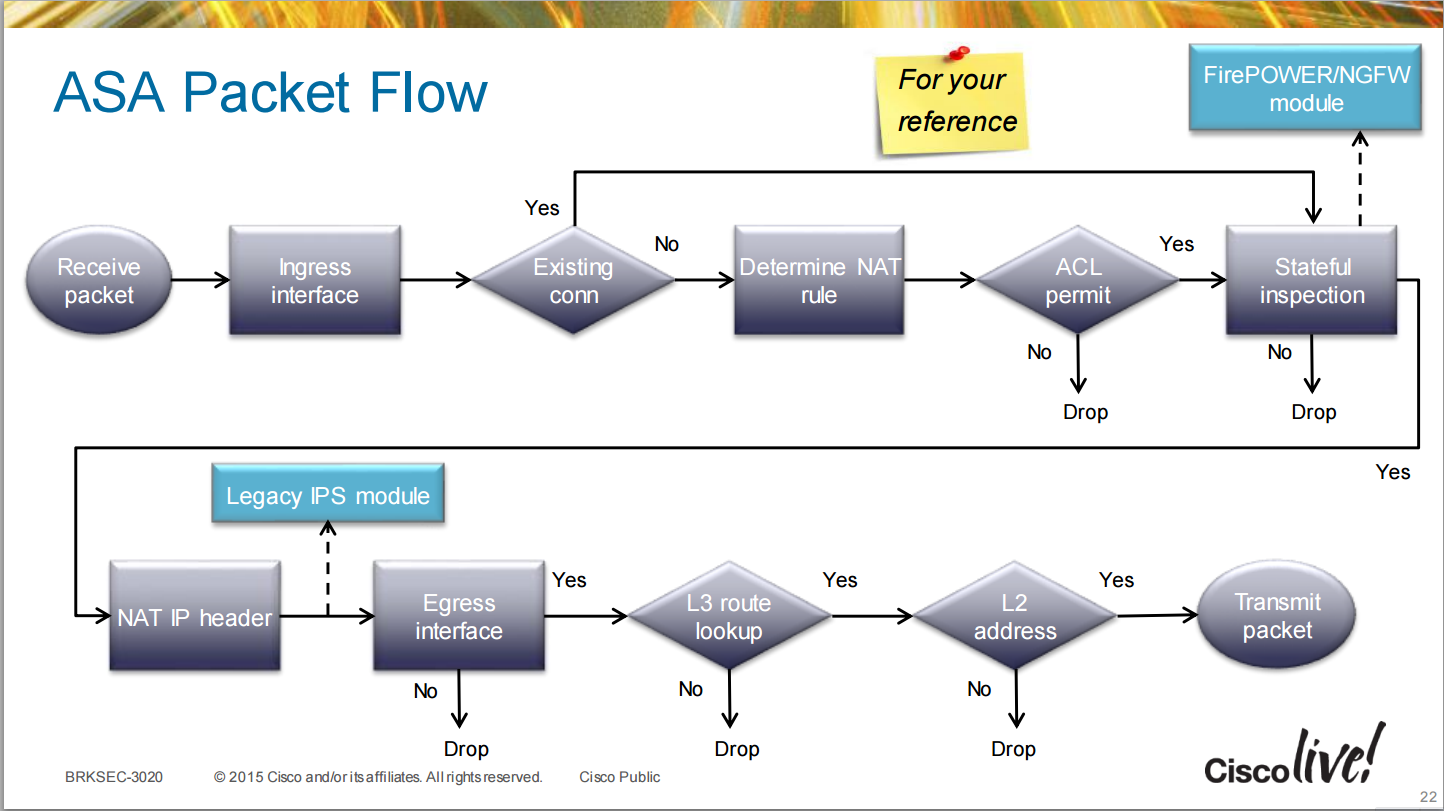
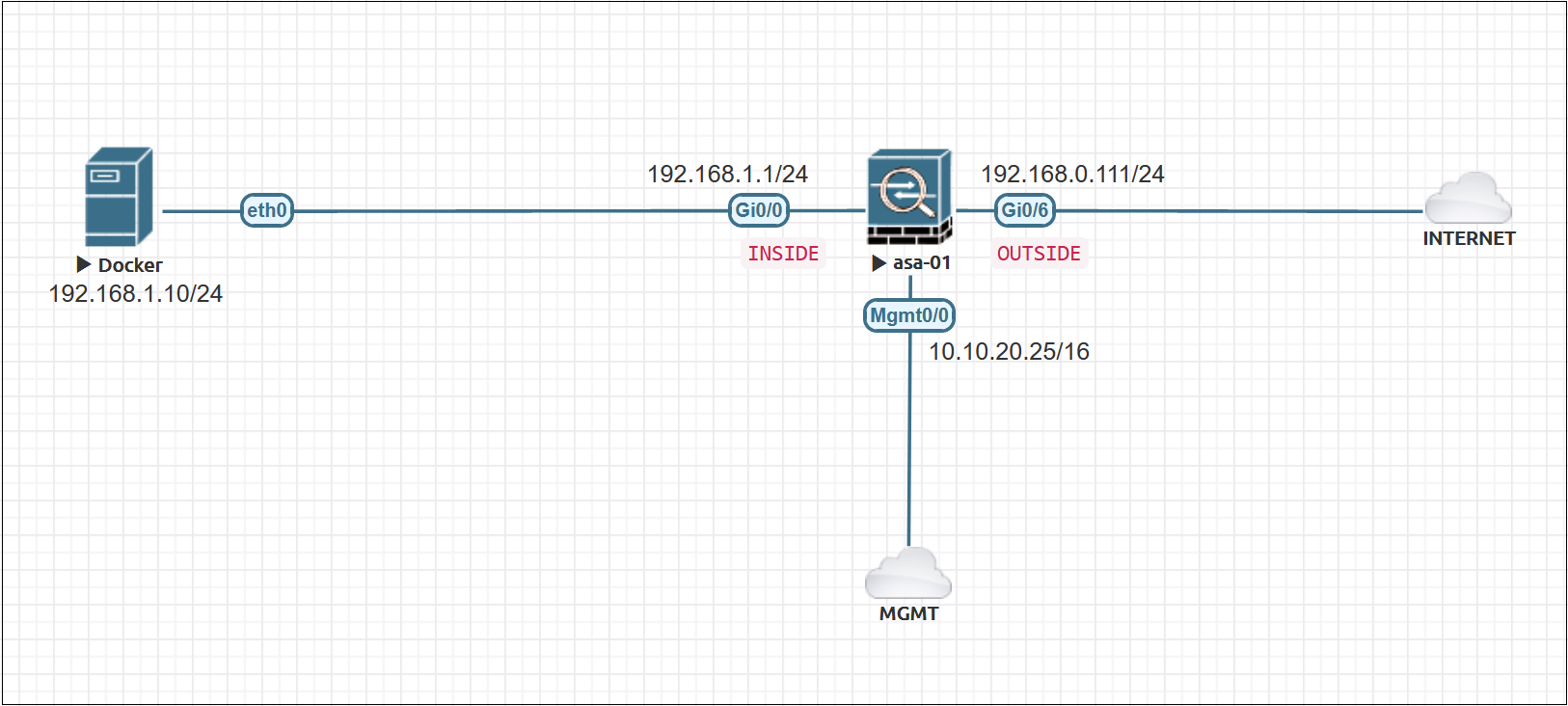
So, a packet arrives. Where does it go? Well, it doesn't just waltz in. Oh no. It hits the input interface first. Think of this as the main gate. Our packet gets scanned right away. Is it even allowed in this part of the castle? The ASA, with its amazing access control lists (ACLs), is already doing its thing. It's like the bouncer saying, "Hold up there, little fella. Who sent you? And what are you carrying?"
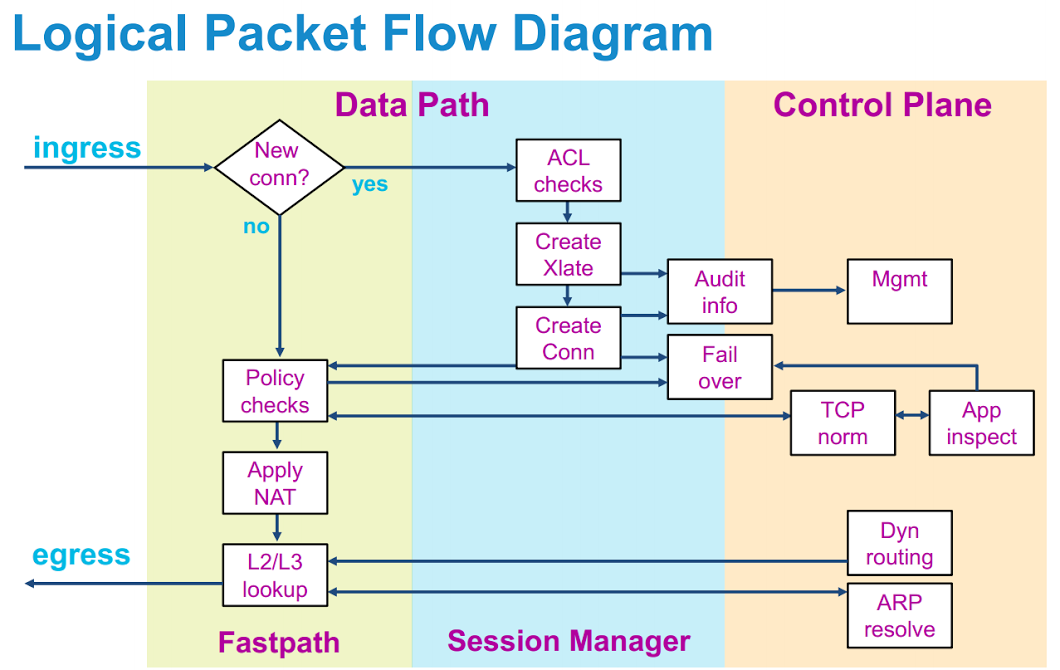
If the packet passes that initial sniff test, it gets to the next stage. This is where things get really interesting, if you're into that sort of thing. The ASA starts doing some serious detective work. It's checking if this packet is trying to sneak through a secret tunnel or a back door. This is where Network Address Translation (NAT) might come into play. NAT is like giving our little messenger a new disguise. It changes the sender's address so the destination doesn't really know where it came from originally. It's all about clever misdirection.
Then comes the part that makes my heart flutter (okay, maybe just a slight twitch). It's the policy lookup. This is where the ASA consults its massive rulebook. Think of it as a chef's meticulously organized recipe book, but for network traffic. This rulebook dictates what happens to our packet. Does it get to go where it's going? Does it need to be inspected further? Does it need to be given a stern talking-to?
And speaking of inspections, this is where the magic of stateful inspection happens. The ASA remembers what packets it's already let through. If a packet is part of an ongoing conversation (like a reply to a question), the ASA is much more likely to let it pass. It's like the bouncer recognizing a regular: "Oh, it's you again! Go on in, just don't cause any trouble." This stateful inspection is crucial. It’s what keeps the bad guys out and lets the good guys (and their important messages) flow freely.
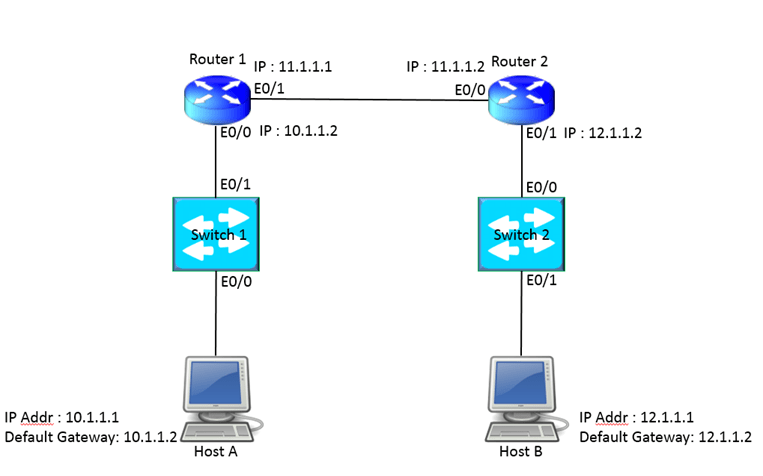
Now, if our packet is trying to start a brand new conversation, things get a bit more scrutiny. The ASA checks its security zones. Imagine different parts of your castle have different security levels. The public courtyard might be less secure than the royal treasury. The ASA ensures packets are only going where they're supposed to, based on these zones. It's all about layered security, like wearing a chainmail shirt under your fancy tunic.
What if the packet is trying to do something a bit dodgy? Like, maybe it’s trying to use a port that’s usually reserved for something else. The ASA, with its understanding of application inspection, can sometimes figure out what’s really going on. It's like a really smart librarian who can tell if you're trying to read a book or use it to hide a secret message. It's a bit of mind-reading for data!
After all this rigorous checking and double-checking, the packet finally gets to its destination within the ASA. This is where it’s decided: does it go out the output interface? Or, is it unfortunate enough to be dropped? The ASA doesn't mess around. If a packet doesn't follow the rules, poof, it's gone. No second chances. It's a tough but fair system, really.
The whole process, from hitting the input interface to potentially exiting the output interface, is what we call packet flow. It's the journey of a digital messenger through the castle gates, past the guards, through the security checks, and hopefully, to its intended recipient. And with Cisco ASA 9.6, this journey is incredibly detailed and, dare I say, a little bit fascinating. It’s the unsung hero of your network, working tirelessly to keep everything safe and sound. So next time you send an email or load a webpage, give a little nod to the ASA. It's probably working overtime for you.
