Describe The Security Risks Associated With Software
Hey there, my tech-savvy compadre! Ever stop to think about all the invisible gears and gizmos that make your favorite apps and programs tick? We love them, right? They stream our shows, let us chat with our pals across the globe, and even help us order pizza at 2 AM. But, like that delicious, yet slightly risky, midnight snack, software can come with its own set of… well, let's call them adventures. Today, we're going to take a peek behind the curtain and have a friendly chat about the security risks associated with software. Don't worry, we'll keep it light and breezy, no need to put on your full-blown hacker hat!
Think of software as a superhero. It’s got incredible powers, making our lives easier and more connected. But even superheroes have a weakness, right? For software, these weaknesses are often called vulnerabilities. They’re like tiny cracks in the armor, little oopsies that sneaky bad guys can exploit. And trust me, there are always sneaky bad guys lurking in the digital shadows, probably wearing too much black and muttering about "exploits."
So, what kind of mischief can these vulnerabilities get up to? Well, it’s a whole smorgasbord of potential problems. One of the most common baddies is malware. You’ve probably heard of it – viruses, worms, Trojans, ransomware… the whole unsettling gang. It’s like the digital equivalent of a contagious flu, but instead of a runny nose, it can steal your data or lock up your computer like a digital ransom note. Yikes!
Imagine you’re downloading a cool new game, or perhaps a "free" PDF of that book you’ve been meaning to read (we’ve all been there!). Sometimes, tucked away inside that innocent-looking download is a little gremlin waiting to cause trouble. This gremlin, or malware, can be programmed to do all sorts of nasty things. It can spy on your keystrokes, meaning it can literally watch you type your passwords. Talk about a privacy invasion!
Then there’s the dreaded ransomware. This one is particularly nasty because it essentially holds your digital life hostage. It encrypts all your important files – your photos, your documents, maybe even that embarrassing karaoke video you swore no one would ever see – and demands a hefty sum of money to unlock them. It’s like a digital kidnapper, and unfortunately, they’re usually pretty good at what they do. The thought alone makes me want to back up my cat pictures religiously.
Another biggie is unauthorized access. This is when someone gets into your software or systems without your permission. Think of it like a burglar picking the lock on your digital house. They might be after your personal information, like your bank details, your social security number, or even just your online gaming account so they can buy themselves some fancy virtual armor. It’s a real bummer when your digital fortress gets breached.

This unauthorized access can happen through all sorts of clever techniques. One that’s quite popular is called phishing. Now, phishing isn’t strictly a software vulnerability itself, but it’s a social engineering tactic that often exploits weaknesses in how people interact with software. You might get a fake email that looks like it’s from your bank, telling you there’s a problem with your account and you need to click a link to fix it. That link, of course, leads to a fake login page designed to steal your credentials. It’s like a digital con artist trying to trick you into handing over the keys to your kingdom. Remember, dear reader, if it sounds too good to be true, or too urgent to be ignored, it’s probably a scam. Your bank probably doesn’t need your social security number via a dodgy link in an email. Just saying!
Speaking of passwords, weak passwords are like leaving your front door wide open with a sign that says "Free Stuff Inside!" They are a major invitation for trouble. If a hacker can guess your password, or use brute-force methods to try millions of combinations (which, thankfully, is becoming harder with modern systems, but still a concern), they’re in. This is why using strong, unique passwords for different accounts is super important. And while we’re at it, let’s not forget about multi-factor authentication (MFA). That’s where you need more than just a password to log in, like a code sent to your phone. It’s like having a double lock on your door – a bit of an inconvenience, sure, but way better than being robbed!
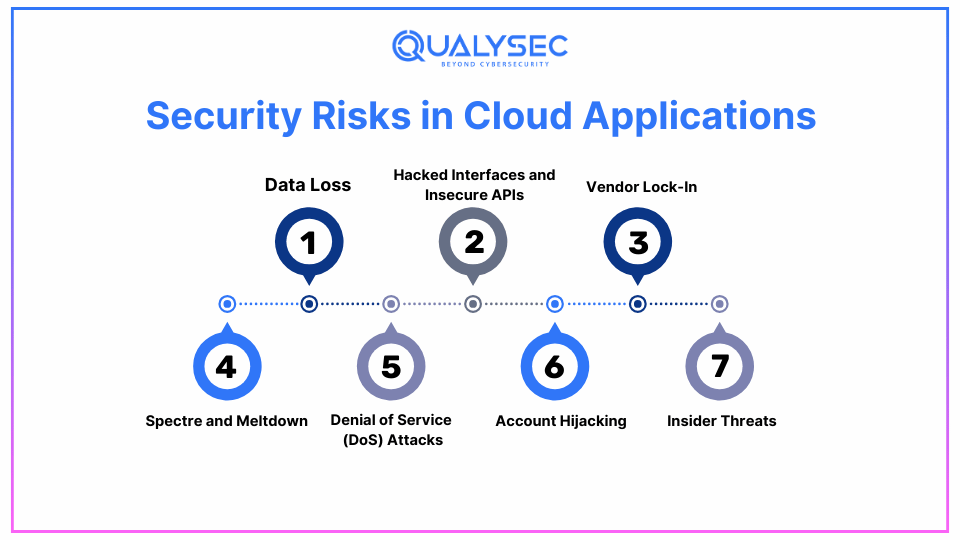
Another area of concern is data breaches. This is when sensitive information is exposed to unauthorized people. It’s like a librarian accidentally leaving a whole shelf of secret files out in the open. Companies that store vast amounts of user data are prime targets. When a data breach happens, your personal information can end up on the dark web, available for anyone to buy and use for nefarious purposes. It’s a scary thought, and it highlights the responsibility software developers and companies have to protect our information.
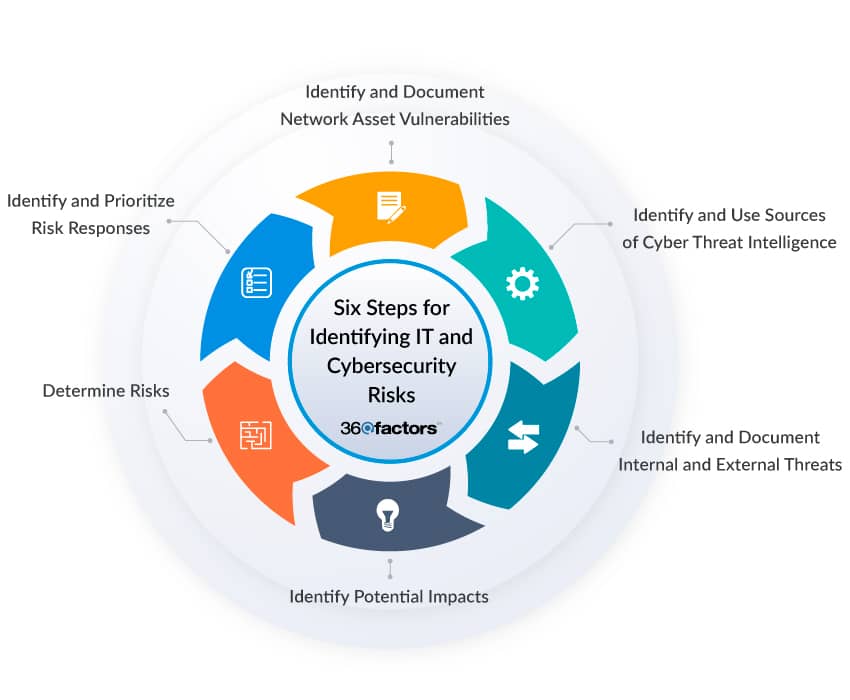
Sometimes, the risks aren’t about malicious attacks, but rather about the software itself being poorly designed or implemented. This is where bugs come in. A bug is essentially a mistake in the software's code. Most bugs are harmless – maybe your favorite game glitches out for a second, or a button doesn't quite work as expected. But some bugs can have serious security implications. They can create vulnerabilities that attackers can then exploit. It’s like a tiny tear in a piece of fabric that, if left unattended, can unravel the whole thing.
Think about legacy systems. These are older software systems that are still in use, often because they’re critical to an organization’s operations. The problem is, these systems were often built in a time when security wasn't as big of a concern, or the threats were much simpler. They might be running on outdated operating systems that no longer receive security updates, making them incredibly vulnerable to modern attacks. It’s like trying to defend a medieval castle with a wooden shield against a laser cannon. Not ideal.
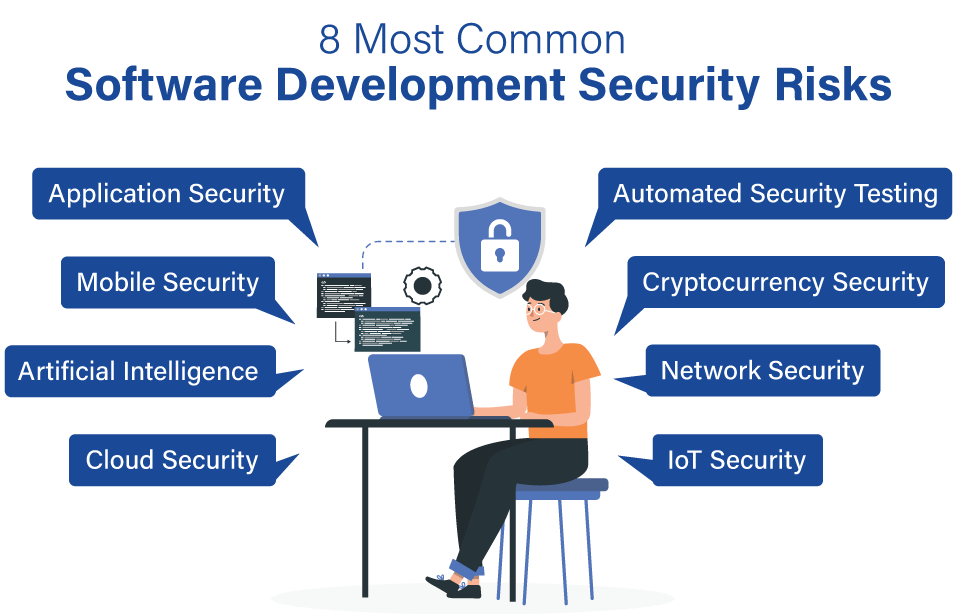
And then there’s the issue of third-party software and libraries. Most software isn’t built from scratch. Developers often use pre-made components, or libraries, to speed up the development process. While this is great for efficiency, it also means that a vulnerability in one of those third-party components can affect all the software that uses it. It’s like a chain reaction – one weak link can bring down the whole chain. This is why it’s so important for developers to keep track of the software they’re using and to ensure those components are up-to-date and secure.

We also need to consider insider threats. Sometimes, the risk doesn’t come from an external hacker, but from someone within an organization who has legitimate access to the software and systems. This could be an employee who accidentally misconfigures a setting, or, in rarer cases, someone who intentionally abuses their privileges. It’s a less common scenario than external attacks, but it’s still a significant risk that needs to be managed.
Denial of Service (DoS) attacks are another fun one. Imagine you’re trying to access a popular website, but it’s suddenly super slow or won’t load at all. That might be because it’s being hit with a DoS attack. Attackers flood the server with so much traffic that it can’t handle legitimate requests, effectively shutting it down. It’s like a massive crowd trying to squeeze through a tiny doorway – chaos ensues!
And what about unpatched software? This is a classic. Developers release updates not just to add new features, but also to fix security vulnerabilities. When you ignore those update notifications, you’re essentially leaving those security holes open for attackers to find. It’s like a doctor telling you to take your medicine, and you just… don’t. Your system might get sick!
It's not just about traditional computers and servers anymore, either. With the rise of the Internet of Things (IoT) – all those smart devices like thermostats, smart locks, and even smart refrigerators – the attack surface has grown exponentially. Many of these devices are built with cost and convenience in mind, and security can sometimes take a backseat. Imagine a hacker gaining access to your smart home security system through a vulnerability in your smart toaster. It sounds like a bad sci-fi movie, but it's a real concern!
So, with all these potential dangers, it’s easy to feel a bit overwhelmed, right? Like you’re constantly being chased by digital ninjas. But here’s the really cool part: the world of software security is constantly evolving. For every vulnerability discovered, there are brilliant minds working tirelessly to fix it and to build even stronger defenses. Developers are getting smarter, security tools are becoming more sophisticated, and the overall awareness of these risks is growing.
Think of it this way: it's not about being perfectly impenetrable, because in the digital world, that's an almost impossible dream. It's about being resilient. It’s about understanding the risks, taking sensible precautions, and knowing that if something does go wrong, there are ways to recover and to learn. It's about building a digital life that's both vibrant and secure, like a well-protected, brightly lit garden.
So, the next time you’re using your favorite app, or clicking on a link, just remember that there’s a whole ecosystem of incredible effort going into keeping things safe. And you, by staying informed and practicing good digital hygiene, are an essential part of that. You’re not just a user; you’re a digital guardian! And that, my friend, is pretty darn awesome. Keep exploring, keep creating, and keep being you, all while being a little bit safer, one click at a time. The digital world is a vast and wonderful place, and with a little care, we can all enjoy its magic with a happy heart and a secure system. Go forth and be digitally brilliant!
