Jmail + Epstein Files: How To Check If A Claim Has A Primary Source

Hey there, fellow curious minds and digital detectives! In today’s whirlwind of information, where news flashes across our screens faster than you can say "deepfake," staying grounded and fact-checking can feel like a Herculean task. We’re bombarded with everything from groundbreaking scientific discoveries to… well, let’s just say more unconventional narratives that tend to make the rounds. And then there are those infamous, highly discussed documents, like the so-called “Epstein Files,” which spark endless speculation and debate.
Navigating this digital ocean requires a good compass, and today, we're talking about a couple of handy tools and a killer technique to help you find your bearings: Jmail and how to sniff out a primary source when you encounter a claim, especially one as potentially explosive as those that emerge from the Epstein saga.
The Jmail Jive: More Than Just Another Inbox
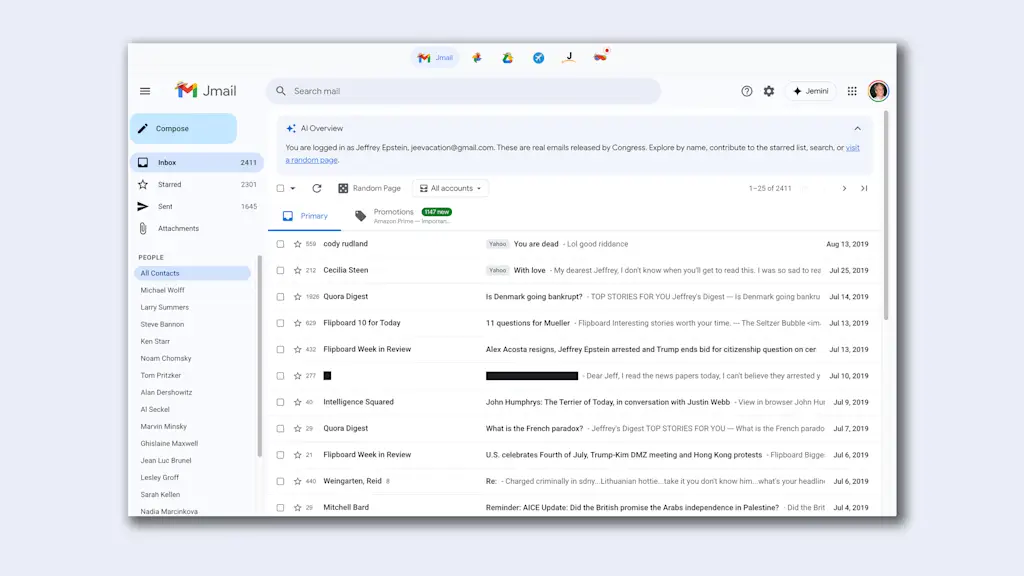
Okay, so what exactly is Jmail? Think of it as your supercharged email client, especially when you're dealing with a lot of communication, research, or even just trying to keep track of your digital life. While it’s not a universally known acronym like "Gmail" or "Outlook," in certain circles and for specific purposes, it refers to more robust, often self-hosted or specialized email solutions designed for serious users. For our purposes today, let's imagine Jmail as your command center for digital correspondence and a starting point for your fact-finding missions.
Why is it relevant to our fact-checking quest? Because often, the seeds of a claim, a rumor, or a piece of information can first appear in private or semi-private communications. Whether it’s an email exchange, a forwarded message, or even a carefully worded statement that finds its way into your inbox, understanding how to manage and analyze these communications is key. Jmail, in this context, represents the organized chaos of your digital life, and we need to bring order to it to find the truth.
The Epstein Files & The Primacy of Primary Sources
Now, let's talk about the elephant in the room, or rather, the files in the… well, you know. The "Epstein Files" have become a sort of shorthand for a complex web of allegations, testimonies, and declassified documents surrounding the disgraced financier Jeffrey Epstein. These files are incredibly sensitive, often containing names, accusations, and details that can profoundly impact reputations and public perception. Because of their gravity, verifying any claim that arises from them is not just good practice; it's absolutely essential.
This is where the concept of a primary source becomes your golden ticket. In journalism, history, and, yes, even in navigating the gossip mill, a primary source is firsthand, original material. Think of it as being at the scene of the crime, or hearing it directly from the horse's mouth. It's the raw data, the original document, the direct testimony. For the Epstein Files, a primary source could be:
- An original, unedited court document.
- A direct transcript of a deposition or testimony.
- An original email or communication from the individuals involved.
- A declassified government report directly related to the investigation.
Anything less is a secondary source (a book, an article, a documentary analyzing the primary source) or, worse, a tertiary source (a summary of a secondary source, like a Wikipedia entry without citations to primary material, or even just hearsay).
Your Fact-Checking Toolkit: Practical Steps to Find the Source
So, how do you actually do this? It’s not always as simple as finding a magical "source" button. It requires a bit of digital sleuthing and a healthy dose of skepticism. Here's your practical guide, with a Jmail-esque approach to managing the process:
Step 1: Identify the Core Claim
Before you can find a source, you need to know what you’re trying to source. Is the claim that Person X knew about Y? Is it that Document Z contains specific information? Break down the assertion into its most basic components. If you saw it in an email in your Jmail inbox, highlight the key sentence or phrase.
Think of this like spotting a catchy headline. What’s the juicy bit that’s making you want to know more? For example, a claim might be: "An email from [prominent figure] to Epstein, recently unsealed, details [scandalous activity]." Your core claim is the existence of this specific email and its content.
Step 2: Trace the Information's Path
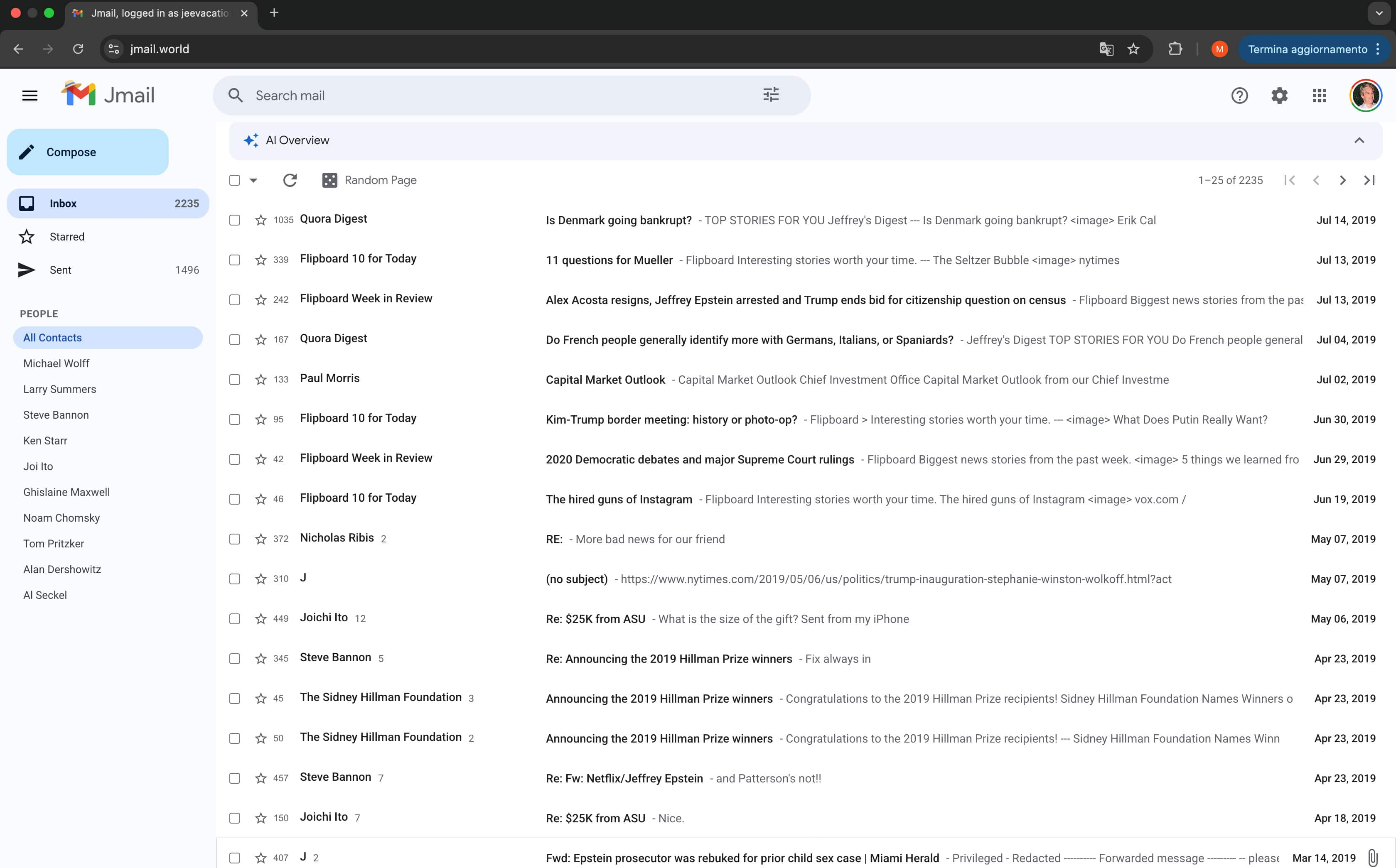
Where did you first encounter this claim? Was it a forwarded email in your Jmail? A link shared in a chat? A social media post that someone linked to? Understanding the initial point of contact is crucial. If it’s an email, is there a chain? Who forwarded it to whom? This is where your Jmail's organizational features (folders, labels, search functions) become your best friend.
Imagine your Jmail as a detective's corkboard, with strings connecting different pieces of information. If an email mentions a document, try to find the original sender or recipient of that document, not just the person who forwarded you the snippet.
Step 3: Look for Direct Quotations or Document References
Claims are often bolstered by direct quotes or references to specific documents. If the claim states, "According to the declassified report, page 73 states...", then that's your starting point! Search for the exact phrasing of the quote or the document name and page number.
This is where cultural savvy helps. Think of it like searching for a specific line from a cult classic movie. If you remember the iconic quote, you can usually find the scene it came from. Similarly, a precise quote from a supposed primary source is a strong lead.
Step 4: The Power of the Search Engine (Used Wisely!)
Once you have a specific quote, document name, or name of an individual linked to the claim, it's time to hit the search engines. But don't just type in the broad topic. Use specific keywords. If you’re looking for a document, try adding terms like "PDF," "declassified," "court filing," "transcript," or the name of the court or agency that would have produced it.
For the Epstein Files, you'd be searching for terms like "Ghislaine Maxwell deposition transcript," "unsealed court documents Epstein," or specific names of individuals involved coupled with "testimony." Be aware that many of these documents are publicly available through official channels, and reputable news organizations will often link directly to them.
Step 5: Verify the Source of the Source
This is the crucial step. If you find a document or a quote, where did it come from? Was it posted on a personal blog with no attribution? Or is it from a government archive, a reputable news outlet with clear editorial standards, or a court website? The origin of the information is paramount.
Consider this: if someone sends you a scanned copy of a supposed secret government memo via email, that’s not the primary source itself. The primary source is the original memo that was officially filed or released. Your friend’s email is a tertiary link at best. You need to find the official release.
Step 6: Look for Official or Reputable Archives
For sensitive and widely discussed documents like those related to the Epstein case, there are often official repositories. Government websites (like court dockets, Justice Department archives, or national archives), reputable news organizations that have published extensively on the topic (and often provide links to source documents), and academic institutions are your best bets.
Think of these as the libraries of the digital age. If a book is worth reading, it’s likely in a good library. If a document is worth citing, it’s likely in an official archive or a trustworthy publication’s archives.
Step 7: Beware of "Leaked" Documents Without Provenance
The term "leaked" can be a red flag. While genuine leaks do happen and can be vital, they are also easily fabricated. If a document is presented as a "leak" without any verifiable chain of custody or confirmation from multiple credible sources, treat it with extreme caution. Who leaked it? Why? Is there any way to confirm its authenticity?
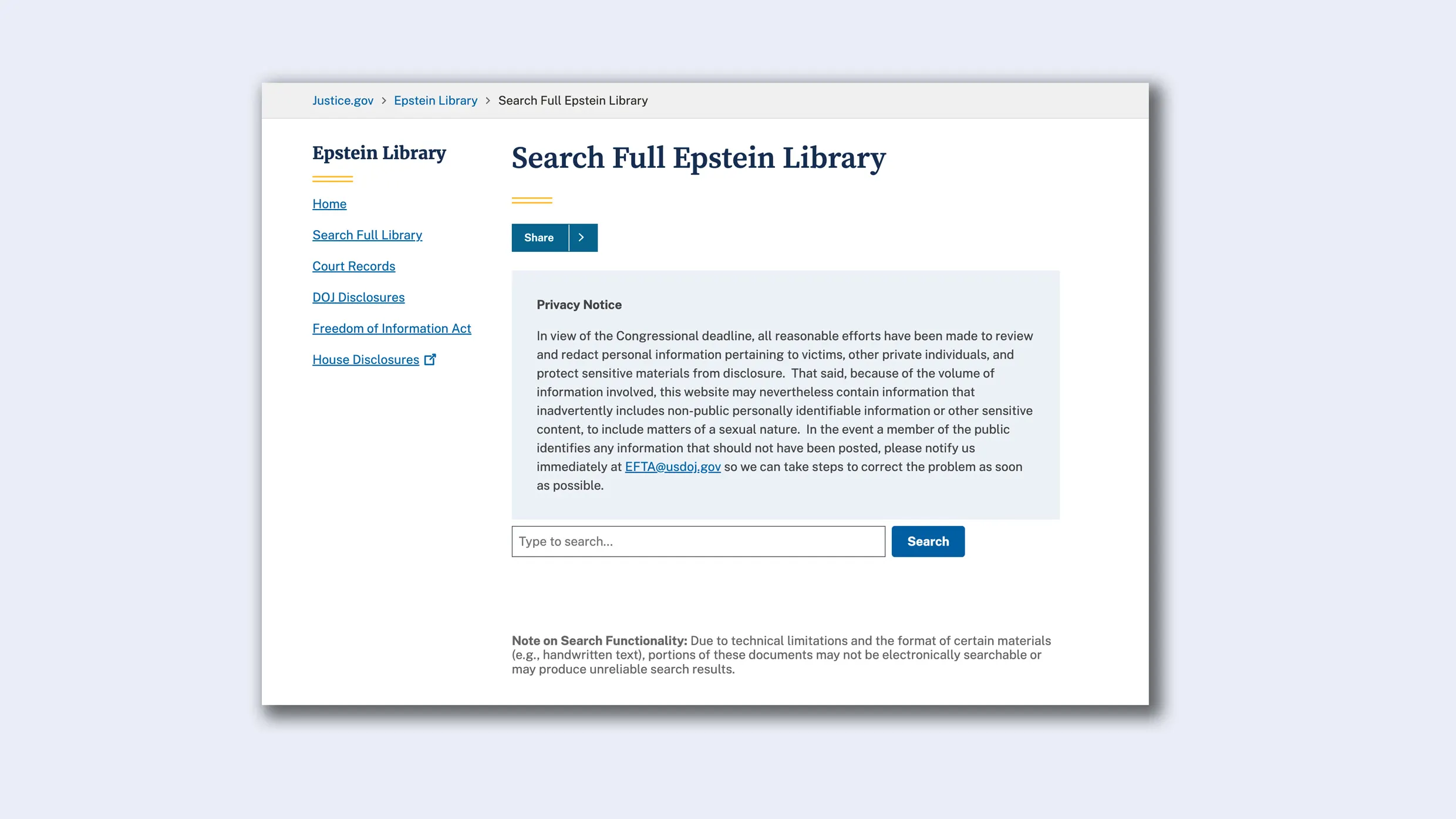
This is like being offered a suspiciously cheap designer handbag on a street corner. It might be real, but the odds are stacked against it. Always seek confirmation from established, reputable sources.
Step 8: Cross-Reference with Multiple Credible Sources
Even if you find what appears to be a primary source, it's wise to cross-reference. Do other credible news outlets or official bodies cite the same document or information? Is the information consistent with other established facts? This helps build a more robust picture and can reveal discrepancies.
Imagine you’re assembling a jigsaw puzzle. If one piece seems to fit perfectly, but it contradicts the shape of its neighbors, you might have the wrong piece. Similarly, if a "source" seems to contradict everything else you know to be true, it’s worth a second look.
Fun Facts and Cultural References to Fuel Your Fact-Finding Fire
- The Gutenberg Galaxy: Did you know that before the internet, the concept of "primary sources" was a bit more contained? Libraries, archives, and historical societies were the gatekeepers. The internet has democratized access but also amplified the need for critical source evaluation. Marshall McLuhan would be having a field day!
- "Trust, but Verify": This famous phrase, often attributed to Ronald Reagan but with roots in Russian proverbs, is the bedrock of good fact-checking. It means assume goodwill but always do your due diligence.
- The "Fake News" Epidemic: The rise of misinformation has made primary source verification not just an academic exercise but a civic duty. Think of yourself as a digital citizen protecting the integrity of information.
- The "Deepfake" Dilemma: As technology advances, even audio and video can be manipulated. This makes verifying the origin and authenticity of digital media more critical than ever. If a video of an Epstein-related event surfaces, where did it originally come from?
- Your Jmail as a Digital Diary: Think of your organized inbox as a personal archive. The emails you send and receive can often be the first threads leading to verifiable information, especially if you're involved in or researching a particular topic.
The Daily Dose of Documentation
You might be thinking, "This sounds like a lot of work. Why bother when the news is delivered to my screen so easily?" And that's a fair question. But consider this: we make countless decisions every day based on the information we consume. From deciding which products to buy, to understanding political issues, to forming our opinions about public figures – it all hinges on the quality of information we receive.
The Epstein Files, with their complex allegations and the ensuing public discourse, are a prime example of how crucial it is to look beyond the sensational headline. They remind us that real people and real lives are at stake, and that speculation can be as damaging as fact. By taking a few extra moments to trace a claim back to its primary source, you’re not just being a smart consumer of information; you're contributing to a more informed and honest public sphere. It’s about empowering yourself with the truth, one verified document at a time. So, the next time you see something that makes your eyebrows shoot up, take a deep breath, fire up your Jmail's search function, and go on a little source-finding adventure. Your brain will thank you for it.
