Sql Injection For Dummies
So, picture this. I'm at this amazing little cafe, right? You know the kind – exposed brick, the smell of roasted beans, a barista who actually remembers your name and your ridiculously specific oat milk latte order. Anyway, I'm tapping away on my laptop, trying to finish up some work, and I decide to order another pastry. Easy peasy, right? Just pop my card details into their online order form. Simple.
Except, this time, something felt a little off. The website was a bit… clunky. Not terrible, but not exactly slick. And when I typed in my name, instead of just accepting it, the little text box seemed to pause for a second, like it was thinking really hard. I shrugged it off, figured it was just a slow server. What could go wrong with ordering a croissant, right?
Well, later that day, my bank calls. "Hi, is this [my name]? We're flagging a few suspicious transactions on your card." My heart does that little thump-thump-thump of panic. I hadn't bought anything else! Turns out, someone had managed to sneakily add a few extra items to my order, and then, get this, somehow used my saved card details to buy… wait for it… 50 lbs of artisanal cat food. Yes, cat food. I don't even own a cat!
My mind immediately went back to that cafe website. That clunky interface. That pausing text box. And that's when it clicked. It wasn't a slow server. It was something far more mischievous, and frankly, a little bit brilliant in a "woah, they actually pulled that off" kind of way. It was a classic case of SQL Injection. And that, my friends, is what we're going to dive into today. No fancy jargon, no intimidating code. Just the plain old truth about how this works, and why you should probably care, even if you're not a coding wizard.
So, What Exactly Is SQL Injection?
Let's break it down. Imagine a website is like a really organized library. It has a catalog (the database) that stores all sorts of information – your user details, product lists, order history, all that jazz. And when you interact with the website, say, by logging in or searching for something, you're essentially asking the librarian (the web application) to go fetch something from the catalog for you.
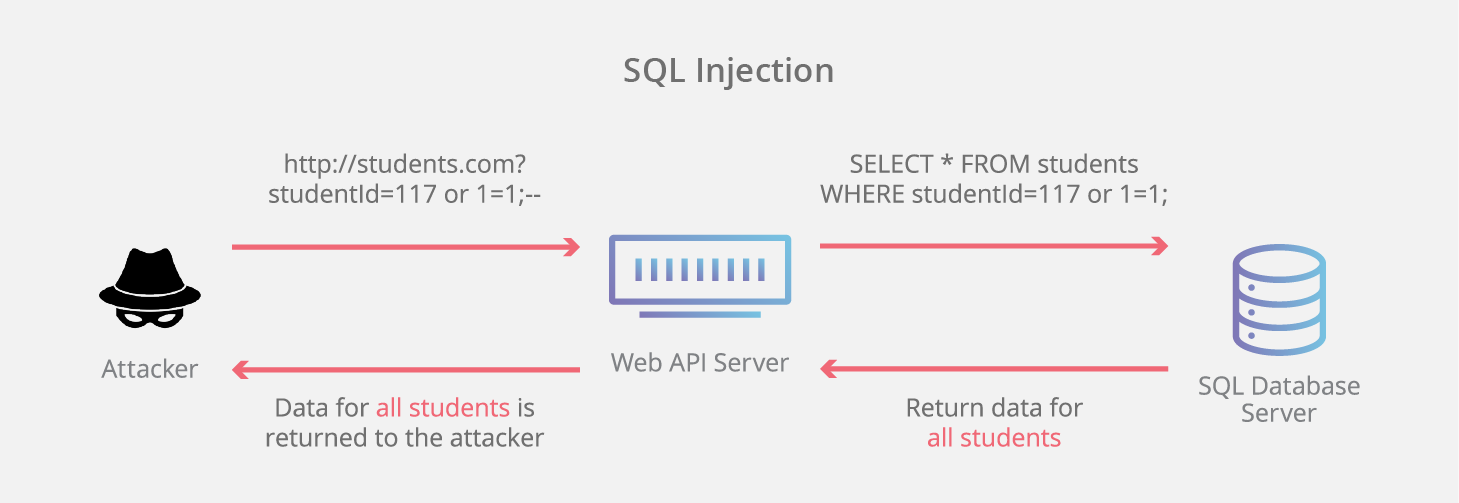
Now, the language that the librarian uses to talk to the catalog is called SQL, which stands for Structured Query Language. It's basically a set of instructions for retrieving, adding, updating, or deleting data. Pretty standard stuff. You tell it "get me the book with title 'The Great Gatsby'", and it does just that.
But here's where things get interesting. What if you could sneak in a little extra instruction into your request? Something the librarian wasn't expecting? That, my friends, is the essence of SQL injection. You're not just asking for a book; you're subtly (or not so subtly) trying to trick the librarian into doing something they shouldn't, like showing you all the secret borrower records or even, you know, ordering 50 lbs of cat food in your name.
Think of it like this: you go to a vending machine and press buttons for a soda. That's a normal request. But what if you could, somehow, press a secret sequence of buttons that made the machine dispense all the snacks, not just one?
How Does This Even Happen? (Spoiler: It's All About Trust)
The vulnerability that allows SQL injection usually arises when a web application doesn't properly validate or sanitize the data that users enter. You know how some websites have those little input fields? Like for your username, your password, your search query, or even your credit card number?
Well, when you type something into those fields, the website takes that input and uses it to build an SQL query. If the website is built securely, it knows what to expect and treats your input as just plain text. It's like saying, "Okay, the user typed 'JohnDoe' as their username. I'll use that specific text to look for a user named JohnDoe."
But, if the website is not built securely, it might take your input and just stick it directly into the SQL query without checking if it contains any special characters or commands. And that's where the magic (or rather, the mayhem) happens.
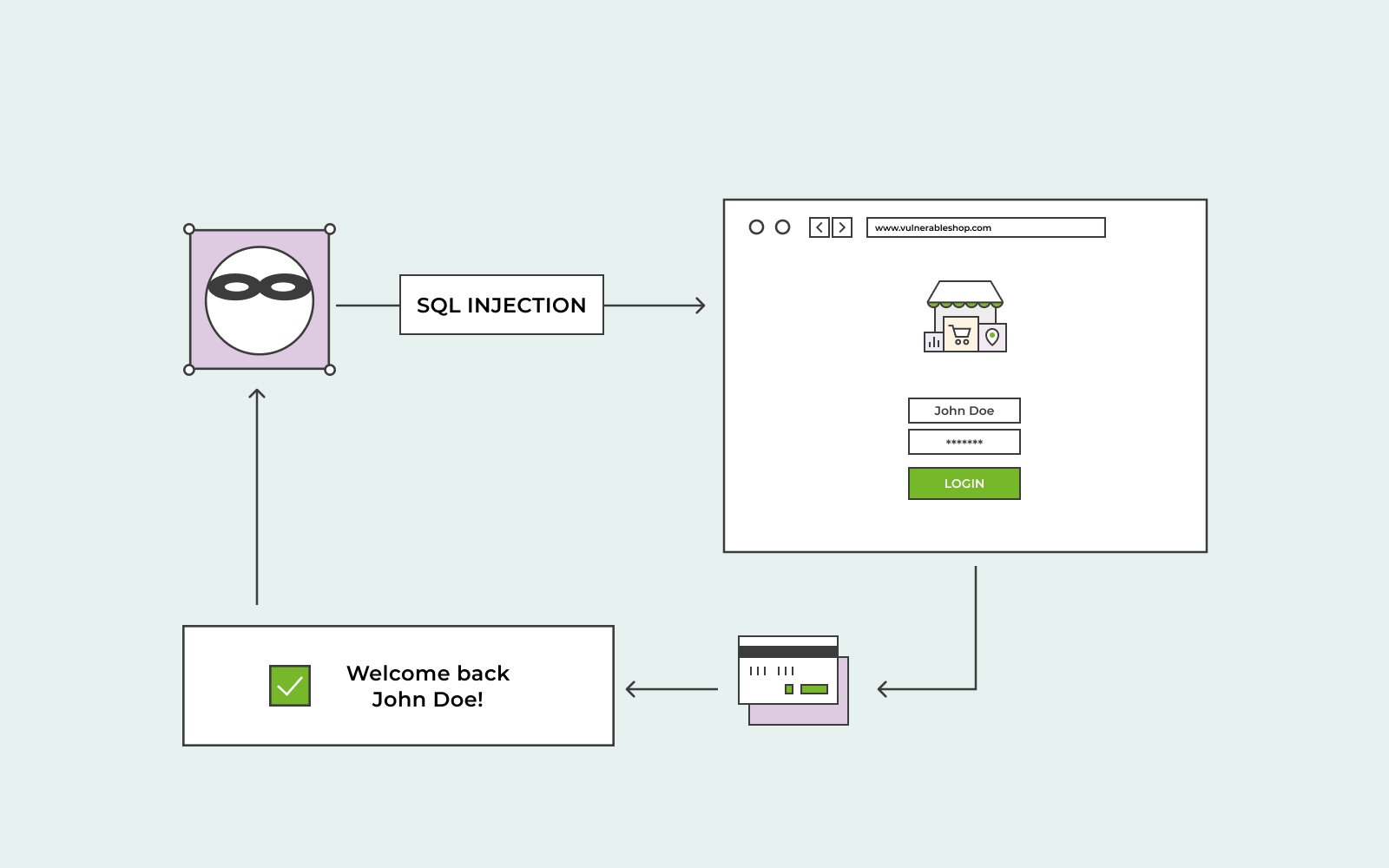
Let's say a website has a login form. Normally, when you enter your username and password, the SQL query might look something like this (simplified, of course):
SELECT * FROM users WHERE username = 'your_username' AND password = 'your_password';
See that `'your_username'` and `'your_password'`? Those are placeholders where your entered text goes. A secure system will treat whatever you type inside those quotes as just data.
Now, imagine a hacker wants to bypass the login. They might try entering something like this into the username field:

' OR '1'='1
What happens to the SQL query then? It becomes:
SELECT * FROM users WHERE username = '' OR '1'='1' AND password = 'your_password';
Whoa! Did you see that? The hacker cleverly inserted `' OR '1'='1'`. Since `'1'='1'` is always true, this condition effectively bypasses the username and password check altogether. The query now says, "Give me all users where the username is empty OR where '1' equals '1' (which is always true)." If the password field is also not properly checked, the hacker might get logged in as the first user in the database, which is often an administrator!
It's like asking the librarian for a book, but instead of just giving the title, you slip them a note that says, "Here's the title you asked for, and by the way, also give me the key to the main vault."
Why Should You Care? (Besides the Cat Food Incidents)
Okay, so maybe you're not a website owner or a developer. You're just a regular internet user. Why should you even bother knowing about SQL injection? Well, here's the thing: every time you log into a website, enter your credit card details, or submit personal information, you're trusting that website with your data.

If a website is vulnerable to SQL injection, it means a malicious actor could potentially:
- Steal your sensitive information: Think usernames, passwords, credit card numbers, addresses, social security numbers – all the juicy stuff that can lead to identity theft and financial fraud. That cat food incident? It was relatively minor. Imagine if it was your bank account details. Yikes.
- Modify data: They could change your account information, alter product prices on an e-commerce site, or even delete critical data. Imagine if someone changed your shipping address to their own for all your online orders. Ouch.
- Gain unauthorized access: As we saw with the login example, attackers can often gain administrative privileges, giving them full control over a website and its database. This is how entire systems can be compromised.
- Deface websites: They might change the content of a website to display offensive material or spread misinformation. It's like scribbling all over the library's beautiful interior.
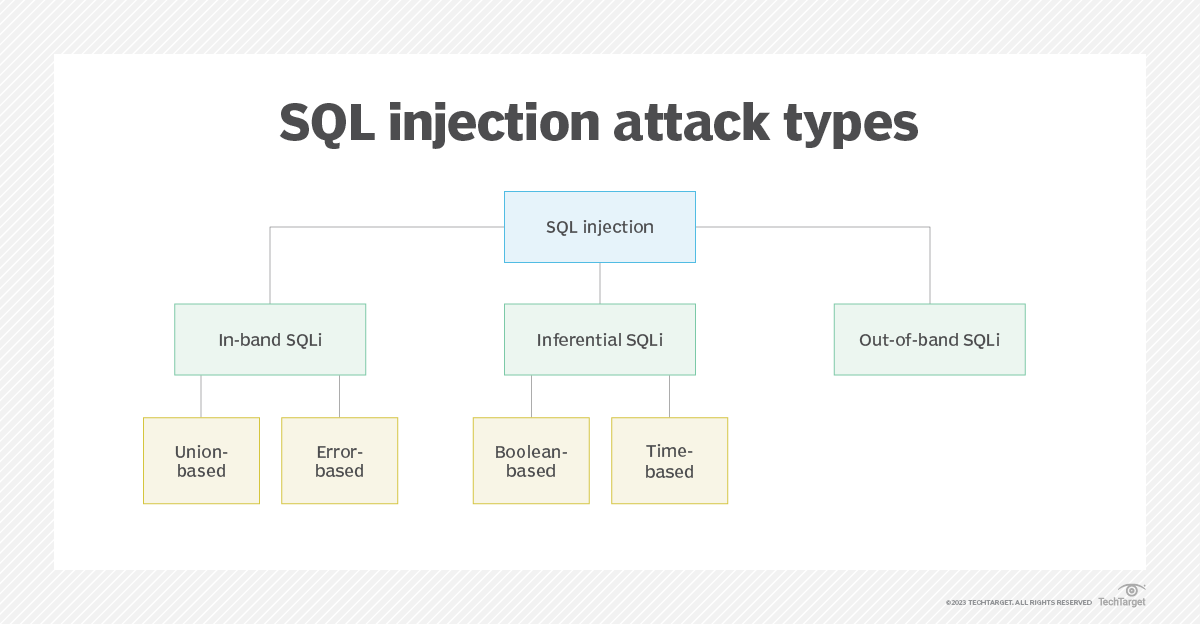
Basically, SQL injection is a gateway to all sorts of digital nastiness. It's one of the oldest and most common web security vulnerabilities, and sadly, it's still very prevalent.
So, How Do We Fight This Evil? (The Developer's Job, Mostly)
Now, for the good news. Developers have ways to combat SQL injection. The primary weapon in their arsenal is parameterized queries (also known as prepared statements). This is the absolute golden rule for preventing SQL injection.
Remember how we saw that the unsafe way was to just stick user input directly into the SQL query? Parameterized queries work by separating the SQL code from the data. Instead of building the query with user input directly, you define the query structure with placeholders, and then you provide the user's input as separate parameters. The database engine then knows, "Okay, this is the command (the SQL code), and this is the data that goes with it." It treats the user's input as just that – data – and never as executable code.
It's like giving the librarian the book title on one slip of paper and the key to the vault on a completely separate, securely sealed envelope. They know which is which and can't confuse them.
Another important practice is input validation. This means checking user input to make sure it conforms to expected formats. For example, if you're expecting a number, make sure the user only entered numbers. If you're expecting an email address, check for a valid email format. This acts as a first line of defense, catching obviously malicious or malformed input before it even gets near the database.
And finally, least privilege principle. This means that database accounts should only have the permissions they absolutely need. The web application's database account shouldn't have the power to delete the entire database if its only job is to fetch product information. This limits the damage an attacker can do even if they manage to inject some code.
What About Us Regular Folks?
While the heavy lifting of preventing SQL injection falls on developers, there are still a few things you, as an end-user, can do to be a bit safer:
- Use strong, unique passwords: This is good practice for all sorts of security reasons, but it means that if one of your accounts is compromised due to SQL injection (or any other vulnerability), your other accounts are still safe.
- Be cautious with untrusted websites: If a website looks a bit dodgy, has a clunky interface, or asks for an unusual amount of personal information, it might be worth being a little wary. Of course, like my cat food incident, even seemingly legitimate sites can have vulnerabilities.
- Keep your software updated: While this is more about browser and operating system security, it's generally good practice to keep everything up-to-date as updates often include security patches.
- Enable two-factor authentication where possible: This adds an extra layer of security, making it harder for attackers to access your accounts even if they manage to steal your password.
Think of it as wearing a seatbelt and checking your blind spot. The car is built to be safe, but those extra precautions can save you in a pinch.
The Takeaway: A Little Knowledge Goes a Long Way
So, there you have it. SQL injection. It sounds scary, and it can be, but at its core, it's about exploiting a website's trust in user input. It's a reminder that the digital world, like the real world, requires constant vigilance and good security practices.
The next time you're filling out a form online, just spare a thought for the humble SQL query working behind the scenes. And if you're a developer? Well, you've got a serious responsibility to make sure your "librarian" knows how to keep those "catalog" secrets safe. Because, trust me, nobody wants to wake up to a surprise delivery of 50 lbs of cat food.
It's a fascinating peek into the invisible battles being fought every second on the internet, and understanding these basic concepts helps demystify a lot of the security headlines we see. Stay safe out there!
